This series “Digital security” is from my notes prepared for certifications.
Asymmetric key cryptography is processing intensive and is suitable only for small bits of data.
Symmetric key cryptography is not expensive (on processing) and can be used to encrypt a very large bulk of data.
Using symmetric key cryptography, ciphertext is as long as the plaintext.
Using asymmetric key cryptography, ciphertext is much longer than the plaintext. Due to this expansion, bulk encryption using asymmetric cryptography is not feasible. This data size difference will translate to processing speed differences which will go on to impact the network’s throughput.
A middle ground in security and performance is achieved by using asymmetric keys to securely share the symmetric keys.
Step 1: Both parties generate their private and public key-pair.

Step 2: Both parties exchange each other’s public keys.

Step 3: ‘A’ wants to send a large amount of data to ‘B’ so it prefers to use symmetric key encryption. ‘A’ encrypts a newly generated symmetric key with B’s public key. B then uses its own private key to decrypt the data and retrieve the symmetric key generated by A. Now the symmetric key has been shared securely over the network.

Step 4: When A wants to send a large bulk of data to B, A encrypts the bulk data with the symmetric key which was previously shared with B. B decrypts the bulk data using the same symmetric key.
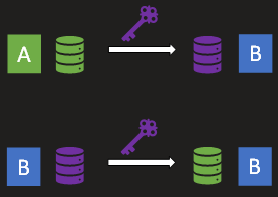
B can use the same symmetric key to encrypt and send data to A.
SSL, TLS, Certificates. IPSec and SSH use SSL which leverages hybrid encryption.