This series “Digital security” is from my notes prepared for certifications.
Asymmetric key cryptography can be used for the purpose of message signatures because:
- The fact that only a public key pair of a private key encrypted message will work, means that the message was encrypted by the owner of the private key. The owner can be uniquely authenticated as a fact of owning the private key.
- The fact that the public key can’t be used by a nefarious actor to encrypt a message and later be used again by another downstream legitimate user to decrypt it, ensures the integrity of the message and security in authenticating the message.
Step 1: A and B generate their asymmetric key pairs.

Step 2: A and B share each other’s public keys.

Step 3: A generates a hash digest of a message using DSA and then encrypts that digest using its private key.

Step 4: A sends the message appended with the encrypted digest to B.
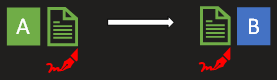
Step 5: B decrypts the appended ciphertext using A’s public key and retrieves the digest. This proves that the digest was encrypted by A using its private key.

Step 6: B then attempts to generate the same digest for the message using the pre-agreed algorithm (mostly DSA).

This proves to B that the message has retained its integrity and wasn’t tampered with in the journey from A to B.
So what’s a digital signature?
In the context of files shared between server and client, it can be the a pre-shared hash of the file. The hash might be in a common location where only the admins can update the hash information.
In the context of SSL/TLS certificates, the public key of one server is already shared with anyone who wants to communicate with that server. So all the tentative clients have that public key. Going by our example, A’s public key is available to B. The public key is just a series of bytes. So A can treat its public key as the message and generate it’s digest. A will encrypt the digest using its private key. The resulting ciphertext is A’s digital signature.
Read the steps again and it might be more clear now.
.